Expressvpn Glossary
FIPS compliance
What is FIPS compliance?
Federal Information Processing Standards (FIPS) compliance refers to the practice of designing systems, products, or processes to adhere to the requirements outlined in the FIPS publications. These standards are developed by the U.S. National Institute of Standards and Technology (NIST) to support the secure handling, processing, and storage of sensitive data.
FIPS compliance can cover a range of requirements. This includes cryptographic modules (FIPS 140 series), Secure Hash Algorithms (SHA), Advanced Encryption Standards (AES), and Personal Identity Verification (PIV). Other security practices may also apply depending on the FIPS publication relevant to the system’s function.
FIPS compliant vs. FIPS validated
FIPS compliance isn’t the same as FIPS validation. A system can be considered compliant when it implements FIPS-approved configurations and uses FIPS-validated cryptographic modules, even if the overall product hasn't been independently tested.
Compliance is typically self-declared and reflects how the standards are applied in an operational environment. Validation, by contrast, is a formal process in which a cryptographic module is tested by an accredited laboratory and validated through the NIST’s Cryptographic Module Validation Program (CMVP). This provides verified assurance that it meets all technical requirements of the standard.
How does FIPS compliance work?
FIPS compliance works through a combination of standardized requirements and organizational implementation: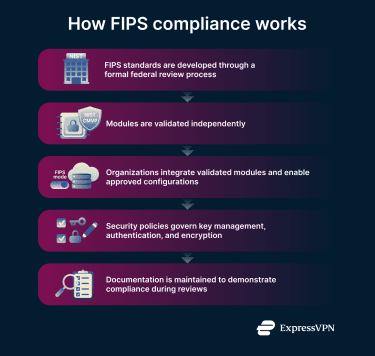
- Standards development: NIST develops FIPS through a federal process that includes public drafts, stakeholder input, and approval by the U.S. Secretary of Commerce. Publications are reviewed periodically and revised or superseded as requirements evolve.
- Selecting validated modules: Organizations use cryptographic modules that have been independently tested by accredited laboratories and validated through the CMVP, as listed in the NIST certificate database.
- Integration and configuration: These validated modules are embedded into software, hardware, or cloud services and configured (for example, by enabling FIPS mode) so that only FIPS-approved algorithms and security functions are used.
- Internal compliance processes: Policies and operational controls ensure proper key management, authentication, encryption, and system configuration in accordance with the federal or regulatory framework that requires FIPS-validated cryptography.
- Documentation and auditing: Organizations maintain configuration records, validation references, and implementation evidence to support audits, assessments, and regulatory reporting.
Why is FIPS compliance important?
FIPS compliance provides multiple security and operational benefits:
- Required in many government contracts: Federal agencies often mandate FIPS compliance for vendors handling sensitive but non-national security information.
- Reduces weak cryptographic configuration risks: Compliance ensures that only standardized algorithms and protocols are used, minimizing misconfiguration or weak encryption.
- Ensures vetted key management practices: FIPS standards cover secure generation, storage, and destruction of cryptographic keys, reducing risks of unauthorized access.
- Supports audits and security assurance: Compliance demonstrates adherence to recognized security practices, helping organizations during regulatory or internal audits.
When is FIPS compliance required vs. commonly used?
FIPS compliance is typically required for U.S. federal information systems, contractors operating those systems, and environments subject to the Federal Risk and Authorization Management Program (FEDRAMP).
Although not required, regulated industries such as healthcare, finance, and manufacturing organizations handling sensitive data may use FIPS-compliant systems to satisfy regulations like the Health Insurance Portability and Accountability Act (HIPAA) or the Gramm-Leach-Bliley Act (GLBA). Finally, software developers, cloud providers, and hardware vendors that supply products to government or regulated industries often implement FIPS-compliant modules to ensure market access.
Further reading
- What are encryption protocols? How they work and why they matter
- What is 128-bit encryption and is it still secure in 2026?
- What is quantum-resistant encryption? (and why it's needed now)


