Expressvpn Glossary
Digital identity
What is a digital identity?
A digital identity is a set of data that uniquely represents a specific user, organization, or device within a given digital service or context, so systems can distinguish one entity from another. It may also be linked to credentials or authenticators that are used to prove control of that identity.
The core purpose of a digital identity is to help enable identification, authentication, and authorization in digital services and transactions.
How does a digital identity work?
A digital identity is formed as a system collects and links attributes to a specific subject over time. In some services, this process can begin before a formal account is created, for example, when a service provider associates device identifiers or activity signals with a browser or device.
When an account is created, these attributes are bound to an account record and may be strengthened through steps such as document checks, verification codes, or identity-proofing processes.
During sign-in (or when reauthentication is required), the system authenticates the subject using credentials such as passwords, biometrics, one-time codes, or security keys. Once authentication succeeds, the system uses the digital identity and its associated attributes (and policy, such as roles) to determine what level of access or permissions to grant.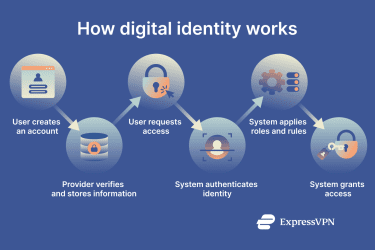
Components of a digital identity
The components of a digital identity can be grouped into several categories (and may overlap depending on the system):
- Identifiers: Usernames, email addresses, account numbers, or government-issued digital IDs that uniquely distinguish a subject within a system or context.
- Attributes: Personal or contextual details such as name, date of birth, contact information, location, behavioral patterns, or preferences that describe the subject.
- Credentials: Secrets and proofs (or records that bind an identity to one or more authenticators), such as passwords, PINs, cryptographic tokens, or biometric authentication factors (often used to unlock or activate an authenticator).
- Metadata: Contextual information about the device, browser, network, geolocation, or login time that can help systems evaluate risk and detect unusual activity.
Why is a digital identity important?
A digital identity helps enable secure online access to services and transactions, often reducing the need for repeated in-person identity checks. It helps verify individuals and organizations for banking, healthcare, government, and other sensitive systems, ensuring that only authorized parties can reach protected information and resources.
Effective digital identity management reduces the risk of unauthorized access and digital fraud, while also supporting privacy, regulatory compliance, and trust across online ecosystems.
Common risks to digital identities
Digital identities are exposed to several recurring risks, including:
- Phishing and credential theft: Deceptive emails, messages, or websites designed to capture passwords, one-time codes, or other authentication data.
- Identity fraud and account takeover: Stolen identity details used to impersonate a person or organization, access services, or perform transactions in their name.
- Weak or reused authentication credentials: Simple, predictable, or reused passwords that make it easier to guess or reuse leaked credentials (credential stuffing) across multiple accounts.
- Data breaches exposing personal details: Large-scale leaks of personal information, identifiers, or credentials that can later be combined and misused for targeted fraud or identity theft.
Further reading
- What is data privacy, and why does it matter?
- Zero-trust data protection explained
- What is two-factor authentication (2FA)?
FAQ
What’s the difference between a digital identity and online identity?
Can a digital identity be stolen?
How can I protect my digital identity?
Using strong, unique passwords for each account and enabling multi-factor authentication (MFA) wherever available helps reduce risk. Keeping devices and software up to date, along with limiting the sharing of personal information or unnecessary account linking, further improves security.
Sensitive accounts are best accessed over encrypted connections. A virtual private network (VPN) service can help protect traffic on untrusted networks by encrypting data between the device and the VPN server and masking the IP address seen by websites, which can reduce some tracking and local-network interception risks.
It is also important to regularly review connected apps, permissions, and account activity to quickly spot and address suspicious access.
Does a VPN protect my digital identity?
However, a VPN does not by itself secure weak passwords, prevent phishing, or stop attackers from abusing data exposed in breaches, so it's only one layer in protecting digital identity.


