What is a DNS flood attack? Understanding its impact and how to prevent it

A DNS flood attack is a type of Distributed Denial of Service (DDoS) attack that targets the Domain Name System (DNS), the service responsible for translating domain names into IP addresses.
By overwhelming a DNS server with a high volume of lookup requests, attackers exhaust its processing capacity or bandwidth, preventing it from responding to legitimate queries. Even if a website’s servers are fully operational, users still won’t be able to reach it because the DNS layer fails first.
Attackers carry out DNS flood attacks for financial gain, competitive disruption, or ideological reasons. In some cases, they demand payment to stop the attack. In others, they aim to damage a competitor’s reputation, interrupt revenue-generating services, or make a public statement. DNS floods may also serve as a distraction, diverting attention while attackers attempt other forms of intrusion.
This guide explains how DNS flood attacks work, why DNS infrastructure is a frequent target, and the technical mechanisms attackers exploit. It also outlines common attack variations and practical strategies organizations use to strengthen and protect their DNS infrastructure.
How do DNS flood attacks operate?
In a DNS flood attack, attackers typically leverage botnets to generate the massive traffic volumes required to overwhelm a server. These botnets often consist of devices like smart cameras, routers, and printers that have been hijacked.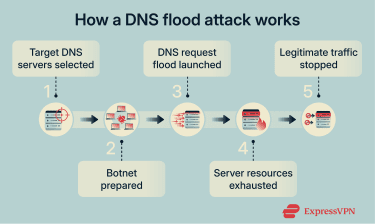
The general lifecycle of a DNS flood attack is as follows:
- Targeting: The attacker picks DNS servers to target. Examples of previously targeted servers include GitHub and services running on AWS or Azure infrastructure.
- Setup: The attacker establishes control of a botnet, which they get from other cybercriminals or build by exploiting vulnerabilities in unprotected Internet of Things (IoT) devices.
- Initiation: The botnet is tasked with initiating a flood of DNS requests to the target server.
- Overloading: The sheer number of DNS requests floods the server, making it much slower to respond.
- Disruption: The overloaded server is unable to respond to legitimate DNS queries, meaning legitimate users are unable to access a website.
Types of DNS flood attacks
Different DNS flood attacks target servers through different means, each exploiting specific vulnerabilities in DNS infrastructure.
NXDOMAIN attacks
NXDOMAIN (Non-Existent Domain) attacks, also known as DNS water torture attacks, flood servers with requests for non-existent domain names. These force extensive resource consumption, as the non-existent domains can’t be cached, and the server has to do a full lookup for them every time. The response for each lookup is an "NXDOMAIN" error.
By sending massive numbers of these bogus requests, attackers can exhaust DNS resources and slow down or disrupt legitimate traffic. Even though each request is small, the sheer volume can overwhelm DNS infrastructure, making websites unreachable and turning DNS into a single point of failure during an attack.
Amplification attacks
Amplification attacks are a type of DDoS attack that use third-party servers or devices to multiply traffic and overwhelm a victim. Instead of sending massive amounts of data directly to the target (like in NXDOMAIN attacks), the perpetrators exploit legitimate internet services to generate much larger responses than the original requests.
These attacks rely on two key techniques: IP address spoofing and protocol abuse. The attacker sends small requests to publicly accessible servers but forges the source IP address so it appears to belong to the victim. The servers then respond to the victim, not the attacker. Because the responses are significantly larger than the requests, a relatively small amount of outgoing traffic from the attacker can turn into a flood of incoming traffic for the target.
Different protocols can be abused in this way. DNS, Network Time Protocol (NTP), Simple Service Discovery Protocol (SSDP), and memcached services have all been used to carry out amplification attacks.
DNS amplification attack
A DNS amplification attack abuses publicly accessible DNS servers to overwhelm a target with traffic. The attacker sends small DNS lookup requests to open DNS servers but spoofs the source IP address so it appears to come from the victim. When those DNS servers reply, they send their responses to the victim instead, flooding the target with data it never asked for.
Attackers often request large responses, causing a much bigger reply than the original request. By sending many of these spoofed requests from multiple systems, attackers can generate massive traffic with minimal effort. Since traffic comes from legitimate DNS servers, it’s harder to block.
NTP amplification attacks
Network Time Protocol (NTP) keeps clocks synchronized across internet-connected devices. Attackers can exploit misconfigured NTP servers by sending spoofed requests with the victim’s IP as the return address. The server then sends its response to the victim instead of the attacker, flooding the target with traffic it never requested.
The amplification part comes from a built-in NTP command called monlist. This command returns a list of up to 600 of the most recent IP addresses that interacted with the server.
When the attacker sends a small monlist request to a vulnerable NTP server, the server responds with a much larger reply, sometimes more than 100 times bigger. This size difference creates the amplification effect.
When attackers repeat this process across many exposed NTP servers, they can generate a large volume of traffic with relatively little effort. That amplified traffic can overwhelm the target’s network or infrastructure, leading to service disruption.
Thankfully, modern NTP versions disable monlist by default, making this primarily a legacy misconfiguration issue.
SSDP attacks
A Simple Service Discovery Protocol (SSDP) attack exploits Universal Plug and Play (UPnP) networking protocols to send an amplified amount of traffic to a targeted victim. UPnP is designed to let devices like printers and smart home hardware announce themselves across a network, and attackers turn this discovery mechanism against a target.
The attacker sends spoofed discovery packets to internet-connected UPnP devices, requesting as much data as possible. Each device then replies to the target's IP address with a response up to 30 times larger than the original request, flooding the target with vast amounts of traffic.
Memcached attacks
Memcached is a database caching system that speeds up websites by storing frequently requested data in memory. Attackers exploit publicly exposed memcached servers by spoofing requests with the target's IP, causing those servers to send large responses directly to the target.
What makes this attack stand out is the scale of its amplification. A 15-byte request can produce a 750-kilobyte response, which is a massive amplification factor that attackers can exploit to launch DDoS attacks against vulnerable services.
The impact of DNS flood attacks
DNS flood attacks lead to various negative consequences for businesses, such as revenue loss, reputational damage, and even regulatory fines following attacks.
When a DNS server becomes overwhelmed, DNS error messages start to appear. If multiple domains share the same DNS provider, a single attack can disrupt all of them simultaneously, leading to widespread outages.
Compromised DNS infrastructure cascades through interconnected systems and applications. The 2016 Dyn attack is a good example of this, where a single overwhelmed DNS provider made dozens of major platforms simultaneously unavailable.
Given the widespread disruption DNS outages can cause, it’s no surprise that the financial impact can be significant. A 2022 study by technology research firm the International Data Corporation (IDC) estimated the average cost of a DNS attack at $942,000 per organization.
Organizations can experience reputational damage and regulatory fines following attacks, too. Long-term effects include potential market share loss and increased insurance premiums.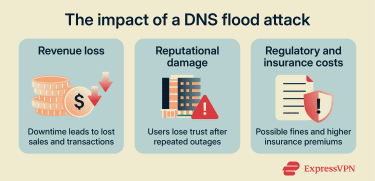
Real-world examples of DNS floods
Over the past two decades, several high-profile incidents have demonstrated how targeting DNS infrastructure can disrupt major portions of the internet.
DNS root server attack
One of the most notable DNS flood attacks occurred in 2002, when attackers targeted the internet’s root DNS infrastructure.
The DNS system relies on 13 root server addresses, labeled A through M, which sit at the top of the DNS hierarchy. While often described as “13 root servers,” each address actually represents a globally distributed network of hundreds of physical servers operated by different organizations. Together, they form the foundation of how the internet directs queries to top-level domain (TLD) servers.
During the 2002 attack, a botnet flooded all 13 root server systems simultaneously with traffic at an unprecedented scale. Nine experienced significant disruption or became temporarily unresponsive.
Despite the severity of the attack, the broader internet continued to function. DNS resolvers cache root server information for extended periods, and because root-level data changes infrequently, most queries did not need to reach the root servers during the disruption. This caching mechanism helped prevent widespread outages.
Dyn
In 2016, the DNS provider Dyn was targeted in a large-scale DNS flood attack that disrupted access to major online platforms and services across parts of North America and Europe.
The attack on Dyn was carried out through a botnet consisting of IoT devices that were infected by Mirai malware.
Some of the notable platforms and services that became inaccessible due to the attack include Airbnb, PlayStation Network, Amazon, Quora, Reddit, GitHub, Spotify, and PayPal.
Best practices for mitigating DNS flood attacks
Effective DNS protection requires a combination of proactive prevention alongside effective incident response capabilities.
Preventative measures
Implementing proactive security controls reduces attack surface and strengthens DNS infrastructure resilience, forming the first line of defense against DNS flood attacks.
That said, before even configuring mitigation procedures, it’s important to ensure that DNS software is kept updated to protect against known vulnerabilities.
DNS server configuration techniques
There are several preventative configuration measures that can help mitigate the impact of DNS flood attacks. Key configuration techniques include the following:
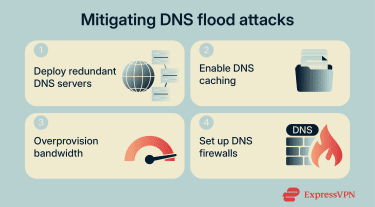
- Ensuring redundancy: Deploying redundant DNS servers helps distribute load and provide failover capabilities. These are essentially backup servers scattered across various locations that hold copies of DNS records and can help distribute traffic load or take over if a server goes down.
- DNS caching: Having cached DNS records ensures not every request is forwarded to the DNS origin server. Also, even if an attack successfully hinders the performance of a DNS service, cached records can continue to be served without slowdowns.
- Overprovisioning: This forces attackers to generate more traffic to cause disruption. This increases the resources and effort required to launch a successful attack, buying valuable time for mitigation measures to activate.
- Deploying DNS firewalls: DNS firewalls add protection layers by filtering traffic before it reaches servers, recognizing DNS attack patterns, and blocking harmful requests. These systems prevent potential exploitation of DNS-based vulnerabilities while allowing legitimate traffic to pass through.
Traffic monitoring and rate limiting
Beyond configuration, active monitoring and traffic control mechanisms can help detect and respond to attacks:
- Monitor DNS traffic continuously: Ensure active traffic monitoring is in place to detect any unusual patterns in DNS traffic. It’s also worthwhile to consider modern DNS anomaly detection tools that use machine learning techniques to detect suspicious patterns.
- Rate limiting: Rate limiting restricts the number of DNS queries a server processes from single sources within specific timeframes, creating a critical barrier against flood attacks.
- Deploy Response Rate Limiting (RRL): RRL detects repetitive query patterns like NXDOMAIN and limits response rates per client, dropping or truncating replies to throttle DNS amplification attacks and reduce victim impact.
- Utilize traffic scrubbing centers: Traffic scrubbing centers (such as those provided by Cisco, Akamai, or Cloudflare) route all traffic through specialized facilities where malicious packets get filtered before reaching DNS servers.
Regular testing and auditing
Continuous validation, documentation, and system maintenance ensure defenses remain effective against evolving threats. Organizations incorporate the following testing practices to ensure a system is effectively shielded from DNS flood attacks:
- Simulated attack scenarios: Simulated DNS flood scenarios ensure response teams and mitigation tools remain prepared for real-world attacks.
- DNS configuration audits: Organizations can schedule regular DNS configuration audits to confirm that best practices like redundancy, caching, and overprovisioning are being followed.
- Incident response plans: These highlight procedures for notifying the necessary stakeholders of an incident as well as the steps needed to mitigate the impact of an attack.
FAQ: Common questions about DNS flood attacks
Is a DDoS attack illegal?
How can I tell if my DNS is under attack?
- A dramatic and unusual increase in traffic coming from multiple IP addresses across the world.
- DNS query resolution is slowed down or halted entirely due to the high request volume.
- Websites whose DNS records are managed by a certain server might become inaccessible if that DNS server is under attack.
- There can be unusual query patterns, such as an excessive number of requests for the same domain or requests for non-existent subdomains.
- DNS servers may indicate excessive CPU or RAM usage far beyond what’s seen during peak traffic times.
What are common methods to prevent DNS attacks?
It’s also important to monitor DNS traffic continuously to detect unusual patterns early and enable a prompt response to potential incidents. Regular DNS configuration audits help maintain adherence to best practices, and simulating attack scenarios on a routine basis can reveal how well DNS servers would hold up under real-world attack conditions.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN