Customer data protection: Practical steps to keep customer information safe
Every time a customer shares their name, email address, payment details, or physical address with a business, that business takes on the responsibility of protecting that information. It’s required to store it securely, use it only for its intended purpose, and protect it from unauthorized access.
This guide breaks down what customer data protection actually involves and what it takes to do it well. We'll look at the types of data that need protection and the most common ways they get exposed. We’ll also cover a practical framework for building defenses, whether you’re a small business handling hundreds of customer records or a large organization managing millions.
What is customer data protection?
Customer data protection refers to the processes, policies, and technical controls a business puts in place to protect customer data from unauthorized access, misuse, loss, or exposure.
This is typically defined through a customer data protection policy. It sets rules for how a business collects, stores, protects, and manages access to customer information, including how it responds if the data is exposed.
What customer data should be protected?
Any data that can identify, relate to, describe, or be linked to an individual customer should be protected. That includes data stored in internal systems, cloud services, backups, logs, analytics tools, and third-party platforms.
Below are the main categories of customer information that require strong protection.
Personally identifiable information (PII)
Personal identifiers are the details that directly identify a person or make them identifiable when combined with other information. Examples include:
- Full name
- Email address
- Phone number
- Home or billing address
- Date of birth
- Government-issued ID numbers
Financial and payment data
Financial information is among the most sensitive data a business can hold. In many cases, it's subject to specific industry standards that dictate exactly how it must be handled.
This category includes:
- Credit and debit card numbers
- Bank account details
- Transaction histories
- Payment tokens
- Billing records
Account and authentication data
This data enables customers to log into services and access their information. If exposed, it can lead to account takeover and further compromise.
Data in this category includes:
- Usernames
- Password hashes
- Multi-factor authentication (MFA) secrets
- Security questions and answers
- Session tokens
Behavioral and preference data
Behavioral data includes records of how customers interact with a business. This first-party data might not seem sensitive at first, but it can reveal detailed insights about a customer’s habits and interests.
Examples include:
- Browsing history
- Purchase patterns
- Device information
- IP addresses
- Marketing preferences
- Interaction logs
Sensitive and special-category data
Some types of customer information require enhanced protection due to their nature and potential impact if exposed. Depending on jurisdiction, sensitive personal data may include:
- Health information
- Biometric identifiers
- Racial or ethnic origin
- Religious or political beliefs
- Sexual orientation
- Precise geolocation data
Why customer data protection matters
From the customer’s point of view, data protection is about safety, privacy, and control. People want to know that the information they share won’t be exposed, misused, or collected more broadly than necessary.
When a business handles customer data responsibly, it helps customers feel more secure and confident in their relationship with that company. Protecting customer data also directly influences how smoothly a business’s operations run and whether it remains compliant with the law.
Customer trust and brand reputation
When customers share their personal information with a business, they're making a judgment about whether that business can be trusted with it.
A data breach, or even the perception that data isn't being handled responsibly, can erode that confidence quickly.
Financial and operational impact
Customer data breaches can create direct and indirect costs. Direct costs include forensic investigations, system remediation, customer notifications, credit monitoring services, legal consultations, and regulatory fines. Indirect ones can involve lost business, higher customer acquisition costs, and internal resources required to manage the fallout.
Operational downtime can also affect revenue. A serious breach can take systems offline and disrupt customer service, billing, and order processing.
Legal and regulatory consequences
Customer data protection laws establish clear expectations for how organizations collect, process, store, and share personal data.
A structured approach to customer data protection helps businesses align with applicable laws and demonstrate due diligence. This includes maintaining audit trails, enforcing access controls, documenting data retention practices, and responding promptly to security incidents.
Non-compliance can lead to regulatory investigations, financial penalties, and contractual consequences with partners or vendors.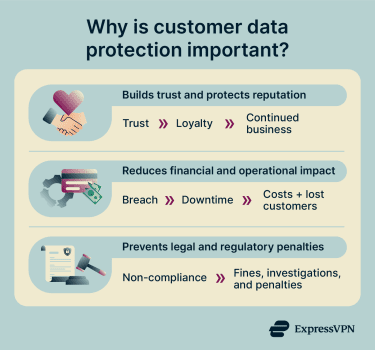
Biggest risks and how customer data gets exposed
Customer data can be exposed in multiple ways, some involving sophisticated attacks and others stemming from oversights. Here are some common exposure paths:
Phishing and social engineering
Attackers send emails and messages that appear to come from a trusted source, such as a bank, a software provider, or a colleague. These deceptive messages trick recipients into handing over credentials, clicking on malicious links, or downloading harmful files.
A successful phishing attack can give a cybercriminal access to internal systems that store personal data, financial records, or account information.
Security awareness training, clear verification procedures, email filtering, and MFA can significantly reduce this risk. However, controls must be paired with ongoing monitoring to detect suspicious activity early.
Credential theft and weak passwords
Stolen or weak credentials are a common cause of unauthorized access to systems holding customer data. Apart from phishing, attackers can also obtain them through purchasing leaked credential lists from previous breaches or brute-force attacks that systematically try common passwords at scale.
A customer or employee using the same password across multiple services can introduce a risk, too. A breach at one platform can provide access to others through a credential stuffing attack.
Businesses can significantly reduce this risk by enforcing strong password management, implementing MFA, and monitoring for unusual login behavior.
Password managers like ExpressKeys make it easier for employees to use unique, complex credentials across different systems without relying on memory.
Misconfigured cloud storage
Cloud misconfigurations can unintentionally expose customer information to the public internet. Common issues include:
- Publicly accessible cloud drives
- Excessive permissions on cloud databases
- Disabled logging or monitoring
- Improperly secured backups
Regular audits of cloud configurations, least-privilege access, clear ownership of infrastructure components, and the use of tools that flag publicly accessible resources are all practical steps toward reducing this risk.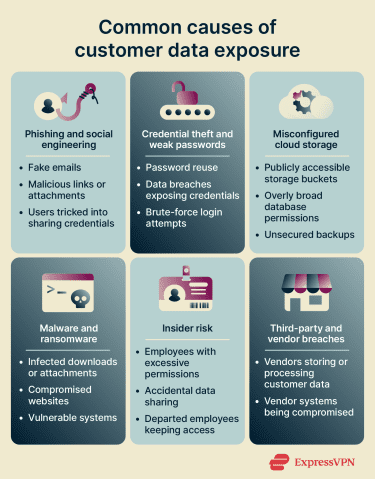
Malware and ransomware
Malware covers a broad range of malicious software designed to infiltrate systems, steal data, disrupt operations, or grant attackers ongoing access.
Ransomware is a particularly disruptive variant of malware that encrypts files or systems and demands payment to restore access. In many cases, attackers also exfiltrate data before encrypting it, giving them additional leverage.
The reputational and regulatory consequences of a ransomware incident involving customer data can be significant, regardless of how the immediate operational impact is resolved.
Timely patching, endpoint protection, network segmentation, and secure backups can limit the operational and financial impact here. Secure backups are particularly important for restoring systems without paying ransom demands.
Insider risk and excessive access
Employees, contractors, partners, and other trusted insiders often have legitimate access to sensitive customer data, which creates both responsibility and risk.
In some cases, misuse is deliberate, like an employee copying the company’s customer database and selling it to a competitor. In other cases, the misuse is accidental, such as when an HR staff member mistakenly sends a spreadsheet with confidential employee information to the wrong email address.
Insider risk typically increases when:
- Users have more access than necessary.
- Access rights aren’t reviewed regularly.
- Departed employees retain active credentials.
- Employees lack proper training on handling sensitive data.
- Data can be exported without oversight.
The principle of least privilege is one of the most effective ways to limit the potential impact of insider incidents. Logging and monitoring user activity also helps detect unusual behavior before it escalates.
Third-party and vendor breaches
Most businesses rely on third parties, such as software providers, cloud platforms, payment processors, marketing tools, and support systems, that have some degree of access to customer data. When those vendors experience a breach, the businesses that share data with them can be affected too, even if their own systems are fully secure.
Under many data protection regulations, companies remain accountable for how their partners handle customer data. If a vendor mishandles or exposes that information, regulators may still investigate the business that shared the data, and customers will often hold the brand responsible.
Vetting vendors before onboarding them, including data protection requirements in contracts, and periodically reviewing third-party access can help reduce exposure to this risk.
A customer data protection framework
Effective customer data protection requires a structured approach that covers the full lifecycle of customer data from the moment it's collected to the point it's deleted. The framework below provides a practical foundation that businesses of any size can adapt to their own environment.
Map where customer data lives
Start by identifying where customer information is collected, processed, stored, and transmitted. This includes internal databases, cloud platforms, Software-as-a-Service (SaaS) tools, email systems, backup repositories, employee devices, and third-party vendors. Additionally, document what type of data each system holds, who has access to it, and how long it's retained.
This step is critical because you can’t protect data you don’t know exists. Without clear visibility, organizations risk overlooking sensitive data, granting excessive access, failing to apply proper security controls, or retaining information longer than necessary, all of which increase the likelihood of breaches, compliance violations, and insider misuse.
Minimize data collection and retention
Excess data increases risk. Therefore, you should only collect the data you genuinely need for defined business purposes. Review forms, onboarding processes, analytics tools, and marketing platforms to confirm that each data field has a clear purpose.
Retention policies are equally important. Define how long customer data should be stored and automate deletion where possible. Align retention schedules with legal requirements and operational needs.
Classify data and set handling rules
A classification system helps apply appropriate safeguards based on the sensitivity of data. For example, basic contact information like names and email addresses may require standard protection, while highly sensitive data such as payment details, government ID numbers, or medical information should be restricted to fewer employees and protected with stronger safeguards.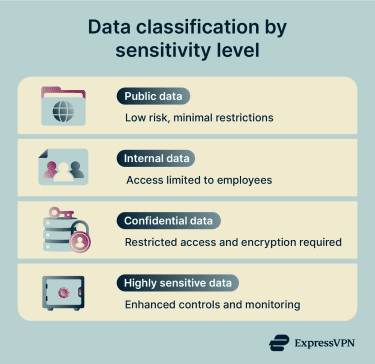
Once data is classified, define handling rules. Specify encryption requirements, storage locations, sharing restrictions, and approval workflows based on data category.
Restrict access with least privilege
Apply the principle of least privilege, which means access to customer data should be limited to those who genuinely need it to perform their role. Avoid broad, shared accounts or permanently elevated permissions. You can implement least privilege through:
- Role-based access control (RBAC)
- Periodic access reviews
- Just-in-time access
- Automated access provisioning and deprovisioning
- Separation of duties for sensitive tasks
Limiting access reduces the risk of insider misuse and minimizes the impact of compromised credentials.
Encrypt data in transit and at rest
Encryption protects customer information from interception and unauthorized access. Data in transit should be protected using secure protocols such as Transport Layer Security (TLS).
Data at rest should also be encrypted using strong standards such as 256-bit Advanced Encryption Standard (AES-256). Many operating systems, databases, and cloud platforms support built-in encryption for disks, storage volumes, and backups. Strong encryption helps ensure that even if storage media is accessed improperly, the information remains unreadable without the correct keys.
Monitor, log, and detect unusual activity
Monitoring and logging create the visibility needed to detect problems early. Use security information and event management (SIEM) systems or similar tools to monitor and analyze activity patterns. Alerts should trigger when anomalies occur, such as large data transfers, access outside business hours, or repeated failed login attempts.
Audit, test, and continuously improve
Audits should assess whether access permissions adhere to the least privilege principle in practice, whether data is deleted in accordance with retention schedules, and whether encryption is consistently applied across all systems that hold customer data. If gaps are identified, they should be tracked and remediated.
Ethical hacking, penetration testing (simulating real attack scenarios to identify cybersecurity vulnerabilities), and tabletop exercises (walking through a simulated incident) can help identify weaknesses in response procedures that wouldn't be apparent from a document review alone. All should be conducted regularly and should inform concrete improvements.
Essential controls and best practices
A customer data protection framework provides structure. Essential controls put that structure into action. The controls below help reduce exposure risk, support compliance, and strengthen business data protection.
Role-based access control
RBAC limits access based on job function. Instead of granting each employee access on a case-by-case basis, access is defined at the role level, and individuals inherit the permissions associated with their role. For example, customer support staff may view account details but not export full customer databases. Finance teams may access billing records but not authentication logs.
Multi-factor authentication
MFA requires users to verify their identity using more than one method before gaining access to a system. Typically, this means something they know (a password), combined with something they have (a code sent to a mobile device or generated by an authenticator app) or something they are (a biometric, like a fingerprint).
MFA is an effective control for protecting customer data because it significantly reduces the risk of unauthorized access due to stolen credentials. Even if an attacker obtains a valid username and password, they still can't access the system without the second factor.
Secure software updates and patching
Unpatched software creates vulnerabilities that attackers can exploit to access customer data. To mitigate this risk, organizations should establish a formal patch management process that includes:
- Monitoring for vendor security updates
- Prioritizing critical patches
- Testing updates before deployment
- Applying updates within defined timeframes
- Implementing compensating controls for legacy systems that can’t be patched
Automated patching tools help maintain consistency. Systems that store or process customer information should receive priority in update cycles.
Endpoint protection
Modern endpoint detection and response (EDR) tools continuously monitor device behavior, looking for patterns that indicate malicious activity, such as unusual process execution, lateral movement attempts, or file encryption consistent with ransomware.
Use endpoint protection alongside device management policies that ensure devices accessing customer data have full-disk encryption enabled and can be remotely wiped if lost or stolen.
Secure backups and recovery testing
Backups protect against data loss caused by system failure, ransomware, or accidental deletion. Best practices include:
- Encrypting backups at rest
- Storing backups separately from primary systems
- Maintaining offline or immutable copies
- Testing restoration procedures regularly
Recovery testing ensures that backup systems work under real conditions. Without testing, backups may fail when needed most.
Data masking
Apply data masking by limiting what users and systems can see. For example, display only the most relevant payment details, redact unneeded personal data in support workflows, and hide sensitive fields in development environments.
Silos with governed systems
Consolidating customer data into governed, centrally managed systems, such as a customer relationship management (CRM) platform or a centralized customer database, reduces fragmentation, where customer data is spread across disconnected systems and inconsistently managed.
Governed systems also make it easier to respond to customer rights requests (the right to access, correct, or delete personal data) within the timeframes required by regulations.
Compliance and customer rights
Customer data protection is closely tied to regulatory compliance, data sovereignty, and individual privacy rights. Laws around the world define how organizations must collect, process, store, and disclose personal data.
Compliance ensures that customers understand how their information is used and can exercise control over it. A well-defined compliance program aligns internal practices with legal obligations and strengthens customer trust.
Build a customer data compliance checklist
A compliance checklist provides a structured way for businesses to assess where they stand against their obligations and identify gaps that need to be addressed. The specific items will vary depending on which regulations apply, but a well-constructed checklist typically covers the following areas.
- Documented customer data protection policy: Does the company have a formal, written policy that outlines how customer data is collected, processed, stored, secured, and deleted?
- Data inventory and mapping: Does the business have a current, accurate record of what customer data it holds, where it's stored, and how it flows through the organization?
- Lawful basis for processing (where applicable): For each category of customer data collected, is there a documented lawful basis? Processing without a valid basis is a compliance failure regardless of how securely the data is handled.
- Privacy notice and transparency: Are customers clearly informed about what data is collected, why it's collected, how long it will be retained, and who it may be shared with?
- Access controls and encryption safeguards: Are there technical and organizational measures that limit data access to authorized personnel only, supported by strong authentication, RBACs, and encryption in transit and at rest?
- Data subject rights procedures: Does the business have documented processes for handling requests from customers to access, correct, delete, or restrict the processing of their data?
- Data retention schedules: Are there defined timelines for how long customer data is kept, along with secure deletion procedures once data is no longer needed?
- Vendor and third-party agreements: Are data processing agreements in place with all vendors that handle customer data?
- Breach response readiness: Is there a documented incident response plan? Does it include notification procedures that meet regulatory timeframes?
- Staff training: Are employees who handle customer data trained on their obligations, and is that training documented and refreshed regularly?
Incident response for customer data breaches
Even with strong preventive controls, no system can eliminate risk entirely. A clear incident response plan ensures that if a customer data breach occurs, the organization responds quickly, consistently, and in alignment with legal requirements.
Detect and triage incidents quickly
Organizations should monitor logs, alerts, and system activity to identify anomalies such as unusual login attempts, unexpected data transfers, or unauthorized configuration changes. Automated detection tools can help flag suspicious patterns in real time.
Once a potential incident is identified, triage begins. This involves:
- Confirming whether a breach has occurred
- Identifying affected systems
- Determining the type of customer data involved
- Assessing whether sensitive personal data was exposed
Clear escalation procedures ensure that security teams, legal advisors, and leadership are informed promptly. Documenting findings from the start supports later reporting and compliance obligations.
Contain and eradicate the threat
Containment steps may include disabling compromised accounts, isolating affected servers or endpoints, blocking malicious IP addresses, and revoking exposed credentials.
Once the immediate threat is contained, teams work to eradicate its root cause. This may involve removing malware, patching vulnerabilities, correcting misconfigurations, or strengthening access controls.
Documentation throughout this phase is important for two reasons. First, it supports the investigation and helps establish a clear timeline of events. Second, it creates the record that regulators, insurers, and senior leadership will need if they're involved later. Notes taken in the moment are significantly more reliable than reconstructions made after the fact.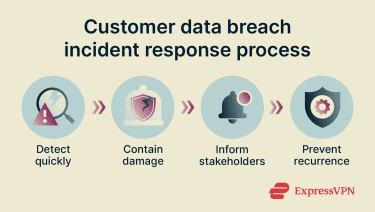
Notify customers and regulators when required
Regulations such as the General Data Protection Regulation (GDPR) and various state-level laws require organizations to notify regulators within defined timeframes if personal data is exposed and risk thresholds are met.
Affected individuals may also need to be informed, depending on the applicable law, the type of data involved, and the level of risk. Customer notification should be clear, factual, and focused on what customers need to know and do. It should describe what happened, what data was involved, what the business has done or is doing in response, and what steps customers can take to protect themselves. Vague or overly reassuring communications that minimize the incident can damage trust more than the breach itself.
Post-incident review and prevention upgrades
A post-incident review can identify gaps in controls, policies, or processes that contributed to the breach. This may include reviewing:
- Access management practices
- Patch management timelines
- Vendor oversight
- Logging and monitoring coverage
- Employee training effectiveness
Use findings to strengthen the customer data protection framework. Update policies, improve technical safeguards, and revise training materials as needed. Testing the updated controls confirms that corrective measures are effective, while continuous improvement reduces the likelihood of similar incidents in the future.
FAQ: Common questions about customer data protection
What are the three main data protection policies?
How can small businesses protect customer data on a budget?
How often should you review access to customer data?
How long should you keep customer data?
What should you do first after a data breach?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN